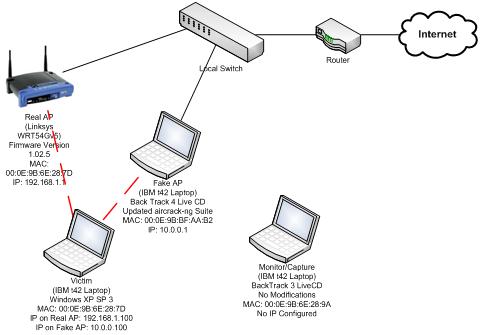
Ethical Hacking wifi hacking | Evil-Twin Attack Part 18 of Ethical Hacking??? #ethicalpakistan #hackingpakistan #blackhathacking #ethicalacademy #Eviltwinattack #fluxion... | By Ethical And Black Hat Academy | Facebook
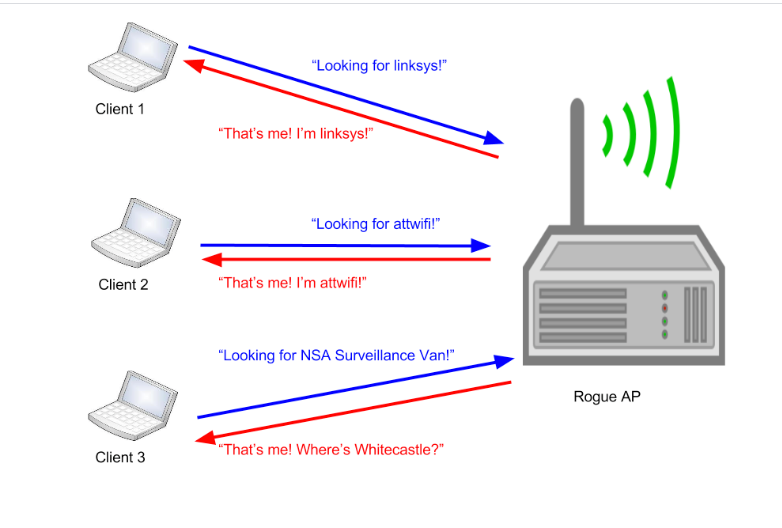
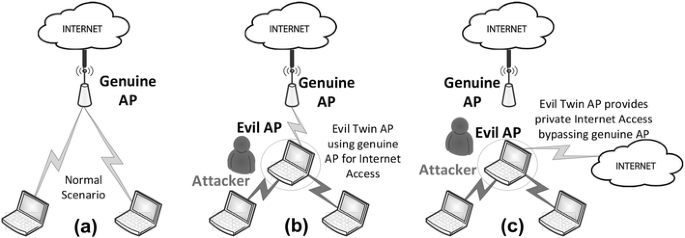
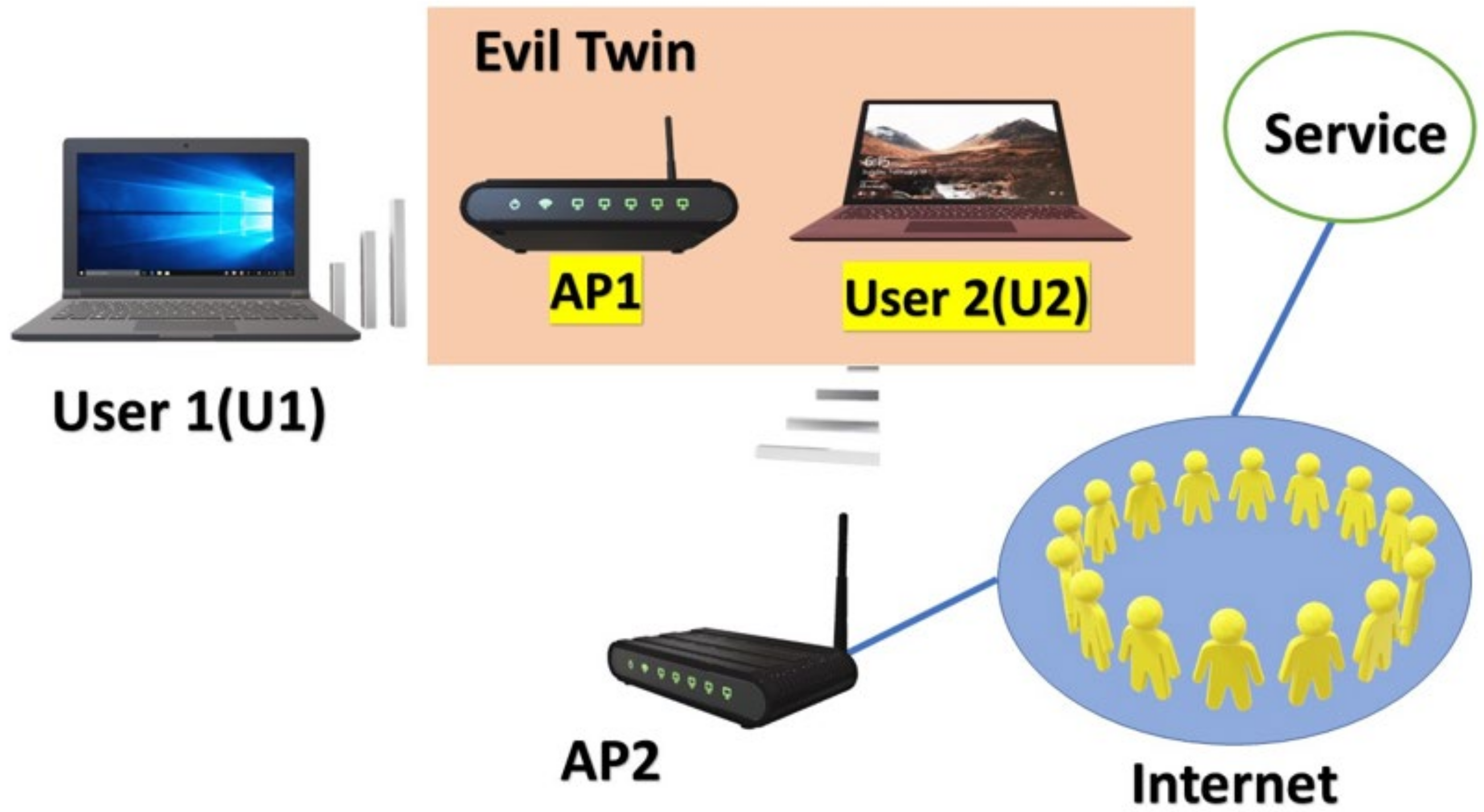
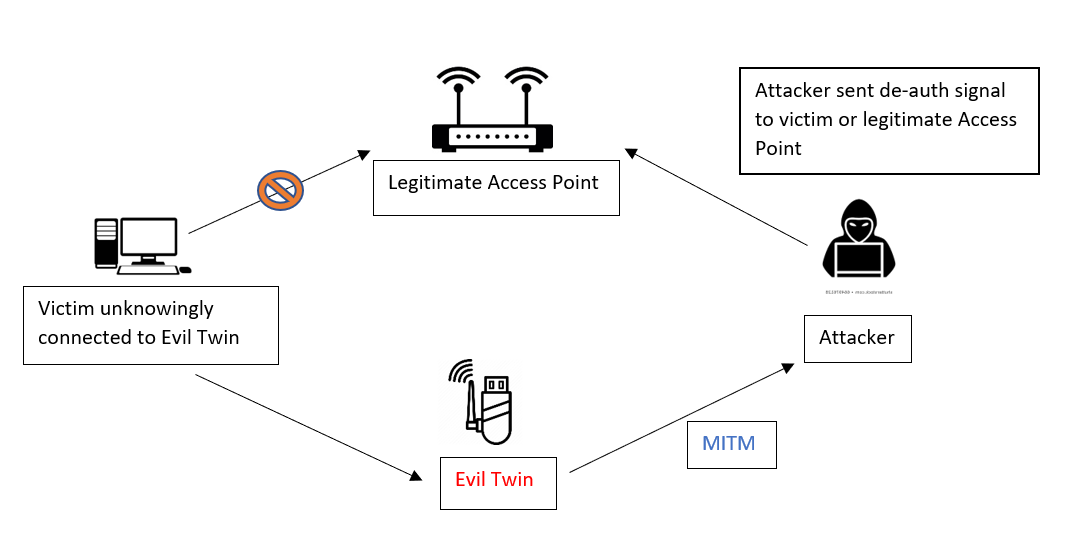
Modern Wireless Tradecraft Pt I — Basic Rogue AP Theory — Evil Twin and Karma Attacks | by Gabriel Ryan | Posts By SpecterOps Team Members

The Verge on Twitter: "The WiFi Coconut is a router's evil twin https://t.co/7ymOXWYQlP https://t.co/htKwstsERf" / Twitter

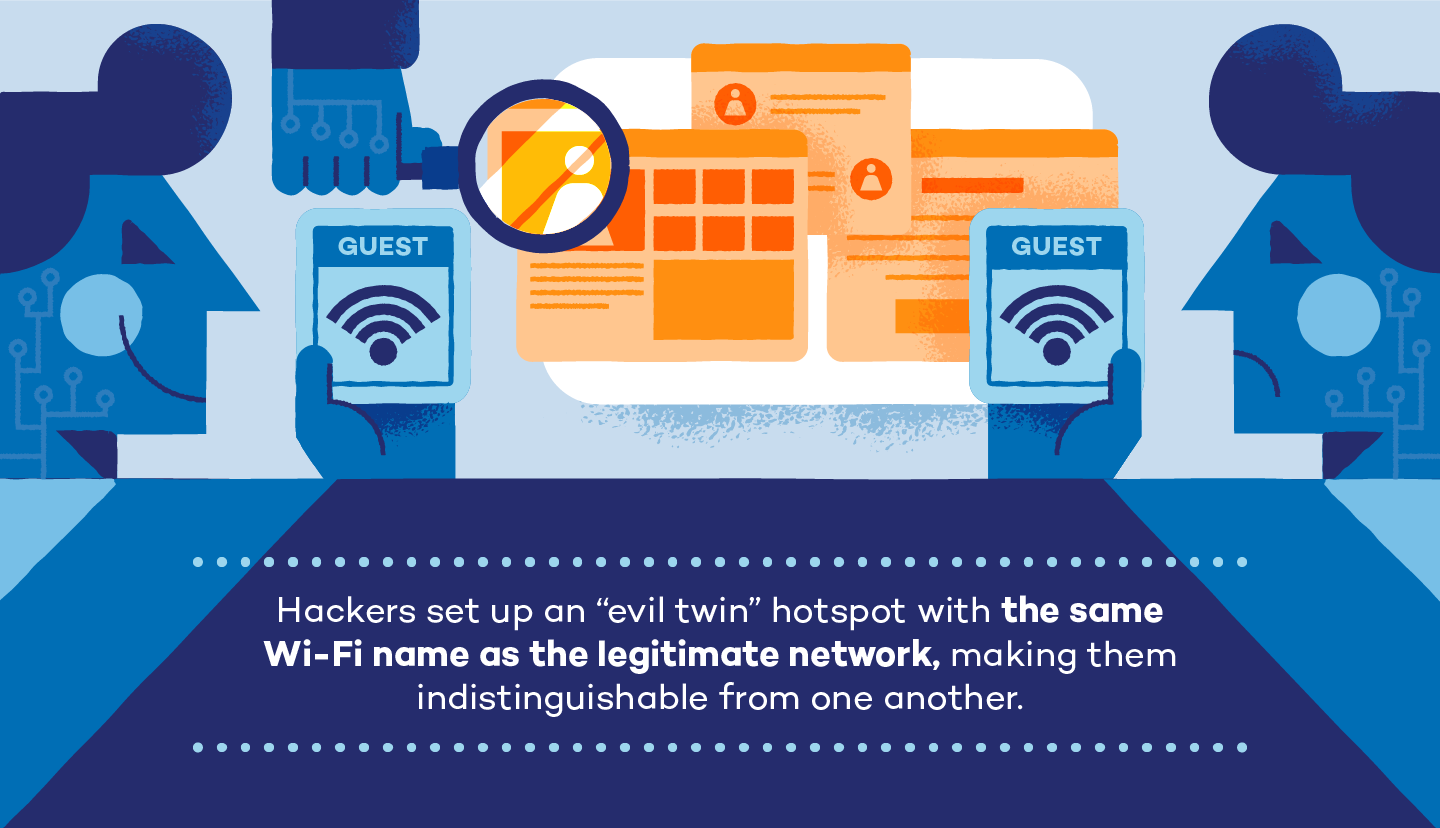
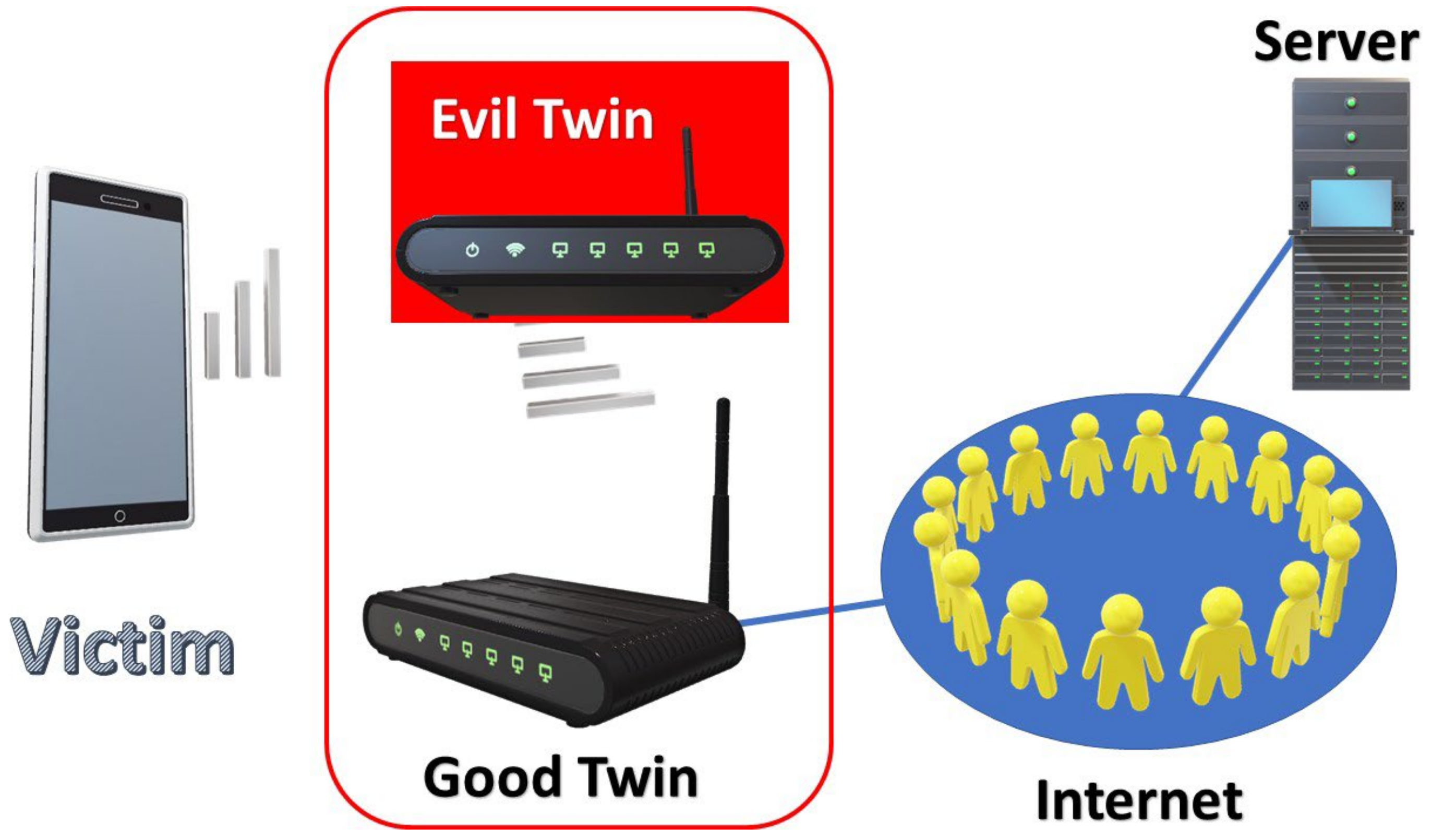
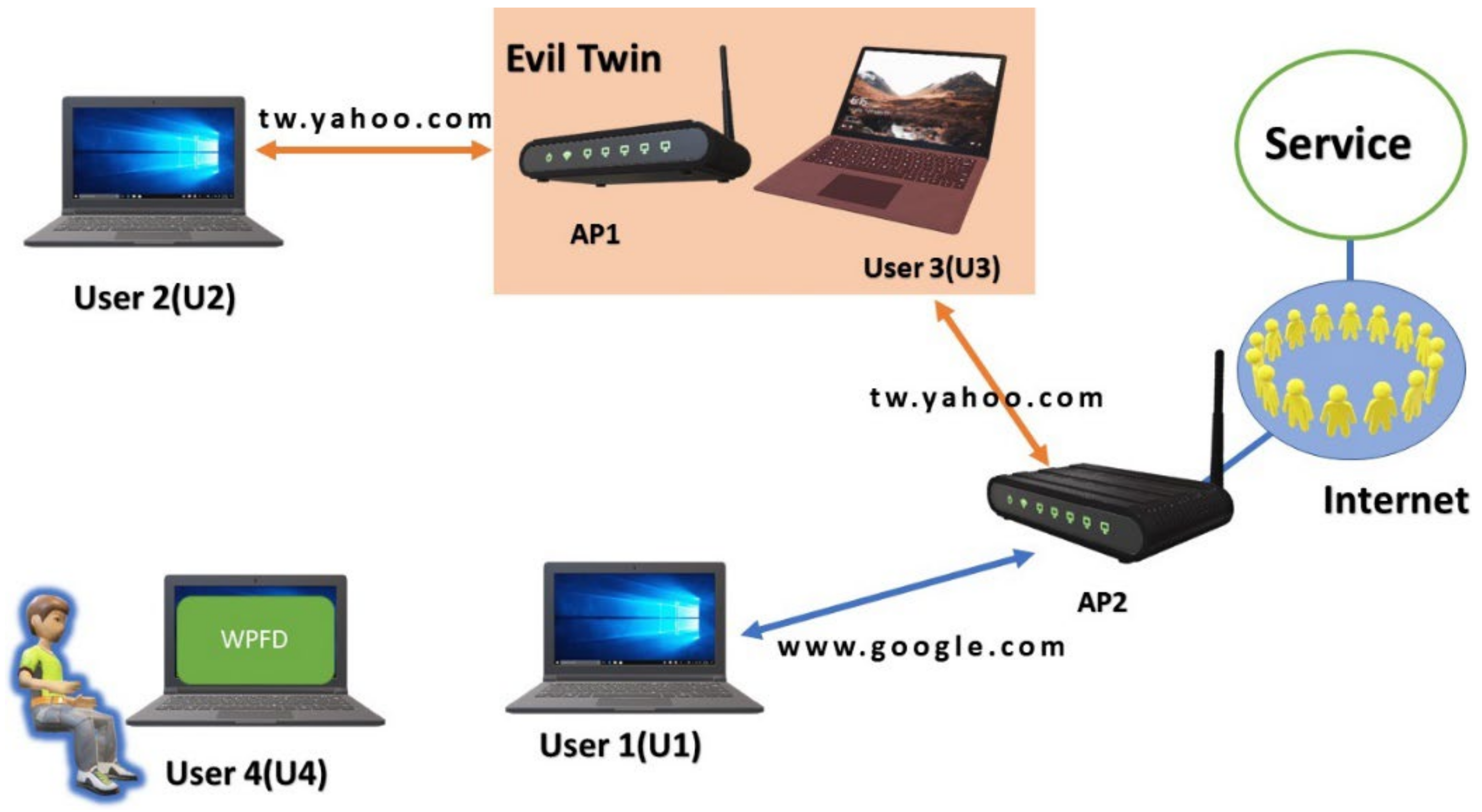
A passive user‐side solution for evil twin access point detection at public hotspots - Hsu - 2020 - International Journal of Communication Systems - Wiley Online Library